The Cybersecurity Assessment Your Insurer, Acquirer, or Board Will Actually Accept
Scored against CIS Critical Security Controls - the same standard our own posture is audited against every year by an independent firm. 20+ years in business. Zero client breaches on record. You get a documented, defensible deliverable - not a vendor opinion dressed up as a report.

What's Included in Our Cybersecurity Assessment Services
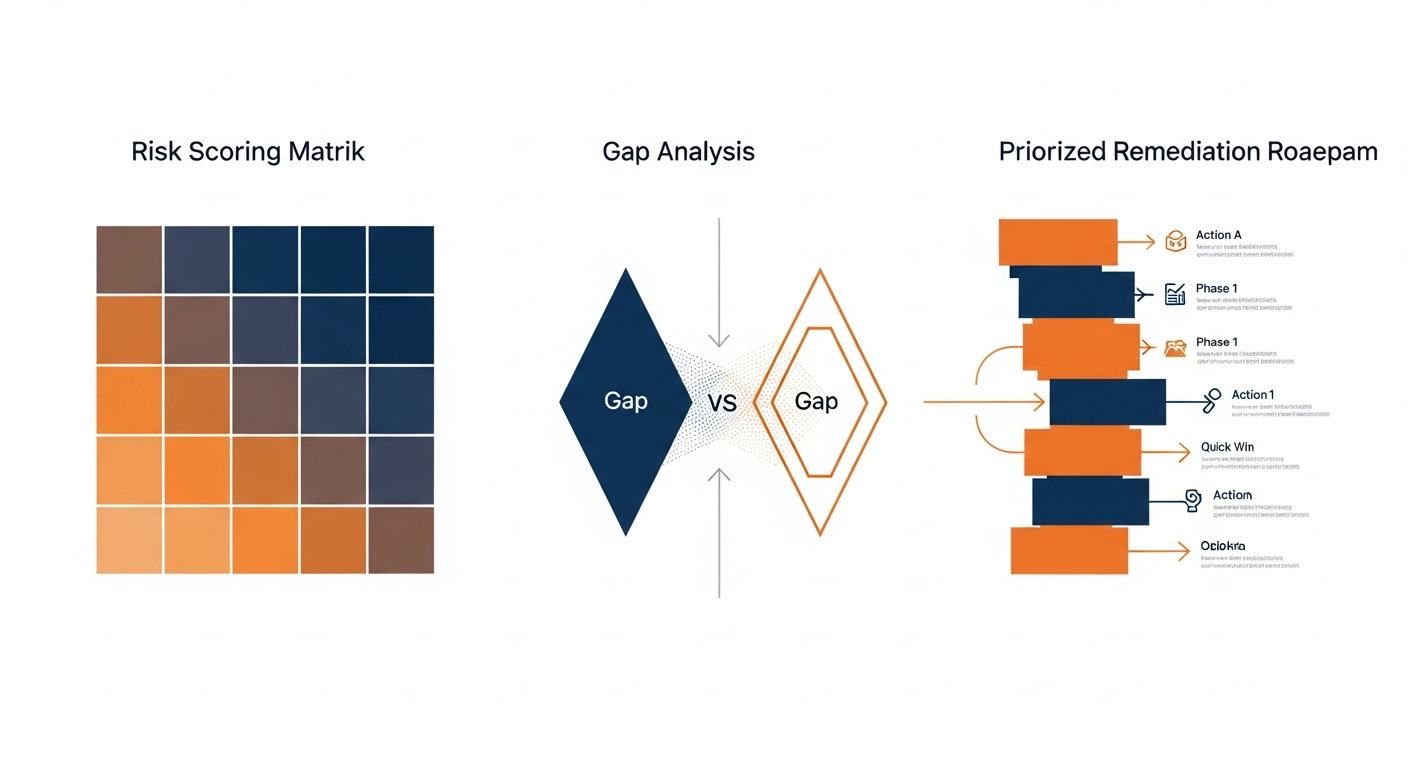
CIS Controls IG2 Scored Baseline
We score your security posture against CIS Critical Security Controls Implementation Group 2 – the recognized mid-market standard – producing a percentage score by control domain. You know exactly where you stand, not just that something is ‘weak.’
Prioritized Remediation Roadmap
Every gap is assigned a risk severity and a remediation priority. Your leadership team receives a sequenced action plan – not a raw findings list with no guidance on what to fix first or why.
Evidence Pack for Third-Party Reviewers
We produce the documentation an insurer, acquirer, or enterprise customer actually needs – methodology, scope statement, findings, and remediation roadmap formatted to satisfy a security questionnaire, diligence request, or audit intake.
Access Control and Identity Review
We examine who has access to what – privileged accounts, multi-factor authentication coverage, and offboarding gaps. Unauthorized access remains the most common root cause of a breach. We find the gaps before an attacker does.
Network and Endpoint Exposure Analysis
We review your network segmentation, firewall configuration, and endpoint protection coverage to identify paths an attacker could use to move laterally through your environment once inside.
Cloud and Data Protection Assessment
We evaluate how your business data is stored, backed up, and protected in cloud environments – including Microsoft 365 configuration posture – so a ransomware event or accidental deletion doesn’t become unrecoverable.
What Forces the Cybersecurity Assessment Conversation - and What You Actually Need From It
Most businesses arrive at cybersecurity assessment services because something external forced the question. A cyber-insurance renewal questionnaire hardened significantly from last year. An acquirer’s diligence team asked for a security posture report. A large enterprise customer sent a vendor security questionnaire as a condition of the contract. A recent near-miss – a phishing email that almost worked, a vendor breach that touched your data – put your leadership team on notice.
Whatever the forcing function, the underlying need is the same: a documented, credible, defensible answer to the question “how secure are you?” – one that holds up to scrutiny from someone who knows what they’re looking at. CISA’s guidance on cybersecurity baseline controls makes clear that a posture review without a recognized scoring framework produces results that are difficult to defend to a third party. A narrative report full of caveats doesn’t satisfy a sophisticated underwriter or an M&A diligence team. A scored baseline, a severity-ranked findings register, and a sequenced remediation roadmap do.
We score every engagement against CIS Critical Security Controls Implementation Group 2 – the framework designed for mid-market organizations with moderate security maturity and meaningful regulatory exposure. This is not a proprietary checklist we invented. It is the same framework our own annual posture is audited against by Versprite, an independent third-party firm. That means we apply the same rigor to your organization that we hold ourselves to – and the resulting report carries the weight of a recognized industry standard, not a vendor-defined rubric a sophisticated reviewer can dismiss.
This engagement is right for businesses between 25 and 500 employees who face a concrete, near-term forcing function: an insurance renewal, an M&A or vendor review, a leadership mandate following a security incident or near-miss, or the start of a formal compliance program. It is also a strong fit for private-equity-backed portfolio companies that need a uniform cybersecurity baseline across multiple holdings. If you also want a regional IT partner to support implementation afterward, see our cybersecurity assessment services for New Jersey businesses.

Get The Ransomware First-60-Minutes Playbook
- ✓What to do in the first hour of an incident
- ✓Decision tree for paying or not paying
- ✓Free PDF - used by our clients in real incidents
No spam, ever. We send you the resource and a short follow-up. Unsubscribe anytime.
How We Deliver Cybersecurity Assessment Services
Scoping and Environment Intake
CIS Controls IG2 Scored Assessment
Findings Report, Scored Baseline, and Remediation Roadmap
Leadership Readout and Next-Step Planning
Take The Cybersecurity Readiness Assessment
- ✓12 questions, ~3 minutes to complete
- ✓Identify your top 3 security gaps
- ✓Personalized risk report by email
No spam, ever. We send you the resource and a short follow-up. Unsubscribe anytime.
Why Businesses Choose Our Cybersecurity Assessment Services
Xact IT Solutions has operated for more than 20 years. In that time we have maintained a record of zero client breaches – a claim that is verifiable and genuinely rare in this industry. Our own security posture is audited annually by Versprite, an independent third-party firm, against CIS Critical Security Controls Implementation Group 2. We hold working expertise across HIPAA, SOC 2, and CMMC – which means we understand not just the technical controls but the regulatory and contractual context in which your assessment findings will land. The NIST Cybersecurity Framework underpins much of the compliance landscape our clients navigate – our team applies that grounding to every engagement. For broader IT support beyond the assessment itself, see our managed IT services.
A typical engagement runs three to four weeks from signed scope to final deliverable. Week one is scoping and intake. Weeks two and three are the active assessment – technical review, documentation analysis, and configuration evaluation. Week four is report production and the leadership readout. You are not handed off to a junior analyst or left waiting. The same senior team members who scope the engagement conduct the assessment and present the findings. We do not use offshore resources or automated scanning as a substitute for human analysis.
In the first 30 days, clients typically experience two things: clarity and relief. Clarity because they have a scored baseline and a ranked list of what actually needs attention – not a vague sense that “cybersecurity is important.” Relief because the deliverable they’ve been dreading – the insurer questionnaire, the acquirer’s security intake, the board presentation – now has a credible, documented answer behind it. By 90 days, clients who engage us for remediation support have typically closed their highest-severity findings and are operating with measurably better visibility into their environment than they had before the engagement began.
Cybersecurity Assessment Services - Frequently Asked Questions
What does a cybersecurity assessment engagement cost?
How long does a cybersecurity assessment take?
What happens on the strategy call?
How are your cybersecurity assessment services different from a typical provider?
Do you serve clients outside New Jersey?
Your Insurer, Acquirer, or Board Is Going to Ask. Have a Defensible Answer Ready.
A 20-minute strategy call with our team – specific guidance you can use immediately, whether you engage us or not. No obligation, no pressure.
Or call us: (856) 282-4100
The Business Impact of Our Cybersecurity Assessment Services
- A posture score your insurer will accept - because findings are documented against CIS Controls Implementation Group 2, not a vendor-defined rubric a sophisticated underwriter can dismiss.
- A diligence-ready evidence pack that shortens M&A timelines - because your acquirer or investor receives a structured, methodology-backed report rather than a collection of ad-hoc answers.
- A prioritized remediation roadmap your team can act on immediately - findings are ranked by severity and sequenced by implementation effort, not listed alphabetically with no guidance.
- Confidence at the board or leadership level - your executive team leaves the readout session knowing exactly where you stand, not carrying a vague sense that 'things need to improve.'
- A scored baseline you can return to - a documented starting point against which future improvements or re-assessments can be measured and reported with credibility.
- Reduced exposure before a near-miss becomes an incident - identifying and closing your highest-severity gaps before an attacker finds them costs significantly less than responding to a breach after the fact.
