The malware is still undetected by the majority of anti-virus programs, according to the analysis by virus checking site Virus Total.
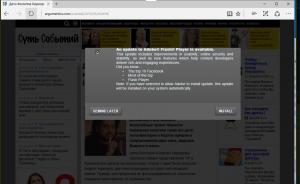
The malware was distributed via a bogus Adobe Flash update.
The outbreak bears similarities to the WannaCry and Petya ransomware outbreaks that spread around the world causing widespread disruption earlier this year.
The new strain of ransomware nicknamed "Bad Rabbit" has been found spreading in Russia, Ukraine, and The U.S.
The malware has affected systems at three Russian websites, an airport in Ukraine and an underground railway in the capital city, Kiev.
The cyber-police chief in Ukraine confirmed to the Reuters news agency that Bad Rabbit was the ransomware in question.
It bears similarities to the WannaCry and Petya outbreaks earlier this year.
However, it is not yet known how far this new malware will be able to spread.
"In some of the companies, the work has been completely paralyzed - servers and workstations are encrypted," head of Russian cyber-security firm Group-IB, Ilya Sachkov, told the TASS news agency.
Two of the affected sites are Interfax and Fontanka.ru.
Meanwhile, US officials said they had "received multiple reports of Bad Rabbit ransomware infections in many countries around the world".
The US computer emergency readiness team said it "discourages individuals and organizations from paying the ransom, as this does not guarantee that access will be restored".



You must be logged in to post a comment.